6 Mainstream Cloud Security Threats
26
OCTOBER, 2017
Cloud security is one of the main reasons why anyone decides to migrate to the cloud. Even though cloud based services do offer exceptionally capable security measures; nothing is absolutely impermeable. There are limitations and there are doorways that the malevolent can exploit. However, as there are complications and restrictions there are also ways to overcome them.
In accordance to the Shared Responsibility Model, Cloud Service Providers (CSPs) are charged only with the security of infrastructure providing cloud backup. The model, doesn’t participate in security settings/monitoring of the operating system. Instead, customers are answerable for security ‘inside’ the cloud or the employment of security controls to protect their sensitive data against security threats.
Cloud security threats
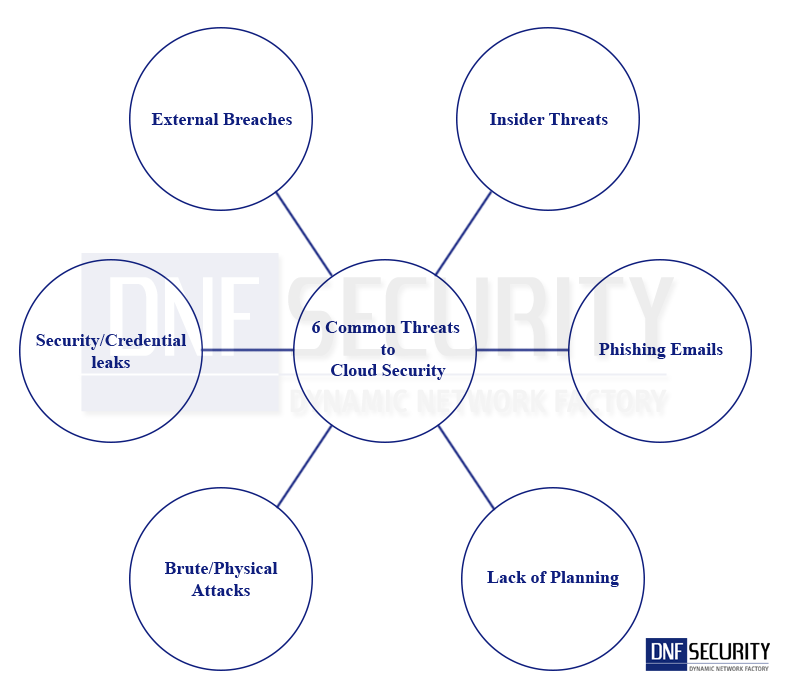
Here are six common threats to cloud security that you need to prepare your cloud backup solution for:
1. Brute Force/Physical Attacks
The vindictive are aware that enterprise cloud environments are often similar in nature to their on-premise infrastructure. These individuals may attempt to leverage open internet to conduct brute force or physical attacks against enterprise backup cloud. In order to prevent this from happening, enterprises need to disable access points to their cloud environments from the open web; such as port 3389 and port 22. Enterprises also need to activate network flow logs and employ best security practices. These practices include but are not limited to, firewall implementation, anti-virus installation and other data analytics and threat monitoring products along with the regular scans of vulnerabilities.
2. External Breaches
If your IT department has a habit of reusing security credentials (passwords, security questions etc.) then it simply does not matter how secure those passwords are kept. For instance, using the same credentials in third party service providers such as Linkedin, Dropbox etc. can lead to a scenario similar to the “mega-breaches” of 2016. The acquisition of credentials from one source can open up the entire world for hackers. This is why enterprises need to unique password protectors and protect their passwords.
3. Security/Credential Leaks
Some IT departments practice hard-coding Application Programming Interface (API) keys, access keys and other important credentials into public source code or documentation. This is obviously a bad idea because hackers can find a way to acquire them. Enterprises need to treat all cloud linked credentials as securely as possibly by never permitting them to move outside the enterprise. It is also a good practice to revise credentials as per a pre-defined schedule (once in three months or once in six months etc.). And the utilization of Multi-Factor Authentication (MFA) adds another layer of security.
4. Insider Threats
Having employees/staff with malicious intent is a challenge that enterprises have to accept and prepare for. Employees may try to acquire sensitive information to sell it to competitors in order to make easy money. However, enterprises can protect their data from these attacks with strict management control and offsite backup. There are also solutions like Amazon Macie that utilize machine learning to learn data access patterns and lock out any unusual anomaly. Another mainstream solution is the Azure Confidential Computing. Azure Confidential Computing addresses this challenge by providing a black box like storage. Storage that focuses on immutable data, so the data that goes in can only be read and that can be controlled by access management as well.
So even if staff with malicious intent does gain access to this data, they can only read it; edits and deletion are impossible.
5. Phishing Emails
Phishing emails are the messengers of the devil. One wrong click can compromise all your sensitive data and enable ransomware to wreak havoc in your local system and all systems over the network as well. Ransomware developers are creating new and frightening ways to attack data. Some ransomware stay invisible and detect data patterns to identify backup locations and then lock up not just the data but also the backup. This is the malicious utilization of machine learning.
This makes phishing emails a serious threat to all backup appliances and cloud based backups. Enterprises can counter the effects by keeping backups on offsite locations with cloud connect services. That way, even if the entire backup infrastructure is compromised, there’s still a way to recover data and not fall victim to the ransomware. Effective recovery from a ransomware depends on the efficiency of your backup and disaster recovery plan.
6. Lack of Planning
It doesn’t matter how efficient and updated your security protocols are if you don’t have an effective plan to utilize them proficiently. Enterprises simply cannot block every single digital threat. It’s very likely that there will be a security breach incident that infiltrates the system despite the advanced security protocols. What’s important at the instance of a breach is what disaster recovery plan does the enterprise have? Or does it actually have one in the first place? The absence of planning can result in chaos. No one knows exactly what to do and data is potentially gone; depending on the scale of the breach, the enterprise may lose millions in revenue, potentially lose clients and suffer serious scars on brand reputation.
In other words, not having a plan is not a good decision. And having a half-hearted plan is also an equivalently bad decision. If the plan doesn’t specifically assign roles and hasn’t been tested, it’s practically pointless.
Conclusion
Enterprises are acquiring enterprise cloud storage to improve their productivity and profitability and to ensure that their sensitive data remains secure. However, no system is a 100% secure. There are a number of threats to cloud services despite their security protocols. The aforementioned common threats provide a general idea of what kind of threats enterprises have to prepare for to prevent data loss.



